Dark web marketplaces explained
Understanding how dark web marketplaces operate helps you recognize real-world cyber risks without glamorizing or engaging in illegal activity. This guide breaks down what they are, how they work, why they matter, and how organizations can protect themselves.
What dark web marketplaces are
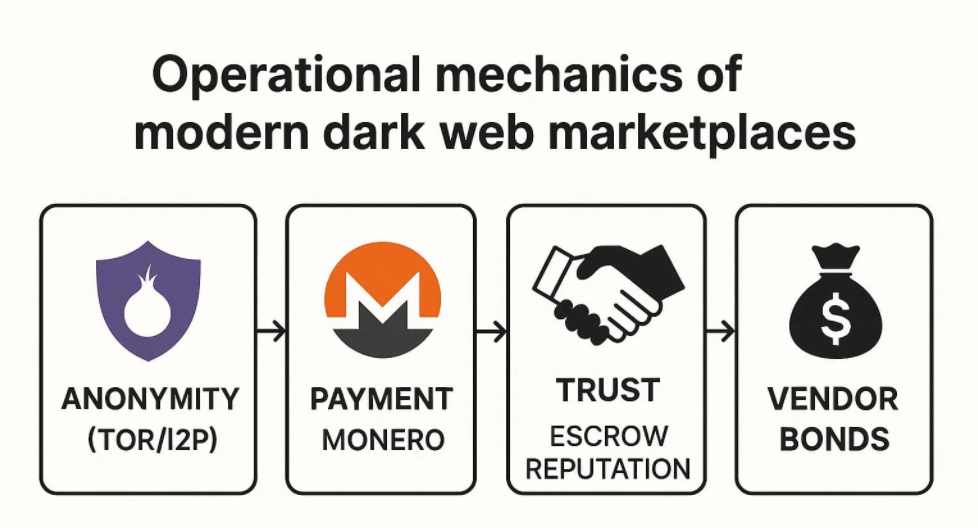
Dark web marketplaces are anonymous, invite-only or semi-open platforms—primarily accessible via the Tor network—where illicit goods and services are traded. Common listings include stolen data, credentials, malware tools, drugs, and fraud services. Most markets use cryptocurrency, escrow, and reputation systems to facilitate transactions and reduce scams for buyers and sellers.
How these markets operate
- Access and anonymity: Markets typically run over Tor with onion addresses, using PGP-based messaging and pseudonymous handles. They rely on cryptocurrency payments and escrow to manage risk and disputes.
- Market dynamics: Ecosystems remain active despite takedowns, with prominent hubs offering multi-purpose products (drugs, data, digital goods) and specialized services (financial fraud, stolen cards, stealer logs). Operations shift frequently due to seizures or “exit scams,” creating a fluid landscape.
- Vendor reputations: Sellers build reputations through ratings and successful trades, while markets enforce rules to keep listings competitive and reduce law enforcement exposure.
Examples of current marketplaces
- Multi-purpose hubs: Abacus and TorZon host drugs, stolen data, and digital goods across global audiences.
- Specialized data markets: Brian’s Club focuses on stolen payment cards; Russian Market and BidenCash trade breached data, credentials, and stealer logs.
- Regional markets: WeTheNorth targets Canadian buyers with localized listings and access models.
- Ecosystem diversity: Lists in 2025 also highlight markets like Awazon and Tor2Door, underscoring constant churn and fragmentation across the scene.
Sources:
What’s being bought and sold
- Stolen data: Payment card dumps, full identity kits, corporate credentials, and stealer logs.
- Fraud services: Cash-out guides, check/ACH fraud, mule recruitment, and phishing kits.
- Malware and access: Ransomware affiliates, initial access to corporate networks, and exploit packs that enable broader cybercrime campaigns.
Why it matters for cybersecurity
- Threat intelligence: Monitoring dark web listings helps organizations detect and respond to leaked credentials, insider offers, or stolen customer data before it’s weaponized.
- Attack enablement: Ransomware-as-a-service and credential marketplaces lower the barrier to entry for less-skilled attackers, increasing the frequency and scale of incidents.
- Supply chain exposure: Vendors and managed service providers may be targeted or unknowingly facilitate attacks via compromised tools sold on these platforms.
Common risks and misconceptions
- Not “too small” to matter: Even small organizations and local institutions appear in credential dumps and stealer logs. Attackers favor volume over single big payouts.
- Churn doesn’t mean safety: Market seizures or exit scams don’t reduce overall risk; activity migrates and reconstitutes quickly.
- Escrow isn’t protection: Escrow only reduces fraud between criminals; it does nothing to mitigate legal, financial, or reputational harm to victims.
Defensive actions for businesses
- Credential hygiene: Enforce multi-factor authentication, password managers, and rapid credential rotation. Continuously check for leaked credentials.
- Data minimization and monitoring: Limit sensitive data retention, encrypt at rest and in transit, and monitor for anomalous access patterns.
- Endpoint and browser hardening: Block stealer malware via anti-malware, EDR, and strict browser extension policies; regularly patch systems.
- Dark web monitoring: Track mentions of your domains, brands, and key personnel to identify potential compromises early.
- Incident response readiness: Maintain tested playbooks for credential leaks, data exposure, and ransomware threats, including legal and communications steps.
Ethical and legal considerations
Accessing or interacting with dark web markets is illegal and dangerous. The only legitimate context is structured, lawful threat intelligence conducted by qualified teams using approved methods. For everyone else, focus on prevention, detection, and responsible response.
Direct answers
- What are dark web marketplaces? Anonymous, Tor-based markets trading illicit goods and data using crypto and escrow.
- Are they still active in 2025? Yes—despite takedowns, several leading marketplaces dominate and frequently shift operations.
- Why monitor them? To identify leaked credentials, stolen data, and emerging threats that can impact your organization.
POWERED BY CYBERGUARD ZW

